Q: What personal data do you collect from users?
We collect your information only with your consent in accordance with our Terms of Service. We only collect personal information that is necessary to fulfill the purpose of your interaction with us. Please see our Privacy Policy for more details about what personal data we collect from users.
Q: Are you GDPR or CCPA compliant?
We're in the process of getting GDPR and CCPA certified.
Q: Do you enforce multi-factor authentication?
Observable uses 3rd party authentication providers (Microsoft, GitHub, Google or Twitter) as well as email login through a one-time-password. Users may have multi-factor authentication configured with their authentication providers.
Q: Do you support SSO/SAML?
We support OpenID Connect with Microsoft and Google. OpenID Connect is a simple identity layer on top of OAuth 2.0. Custom SSO is available for Observable Enterprise customers (learn more). The SAML protocol is not supported at this time.
Q: Is your network traffic handled through HTTPS?
Observable is only accessible over HTTPS and only encrypted HTTPS and websockets (WSS) are used for data transmission. Our commercial certificate is signed by Cloudflare, and we only allow TLS 1.2 and higher for HTTPS connections.
Q: How do you monitor threats and vulnerabilities?
Our production infrastructure is hosted by Heroku, and is contained within Heroku’s secure network. Heroku regularly undergoes penetration tests and vulnerability assessments to ensure that the network remains secure. See: https://www.heroku.com/policy/security.
We also rely on GitHub Enterprise’s advanced vulnerability scanning and security alerts. They monitor our codebase and dependencies for vulnerabilities, and issue automated alerts when problems are found. See: https://github.com/features/security.
Q: How do you protect user data?
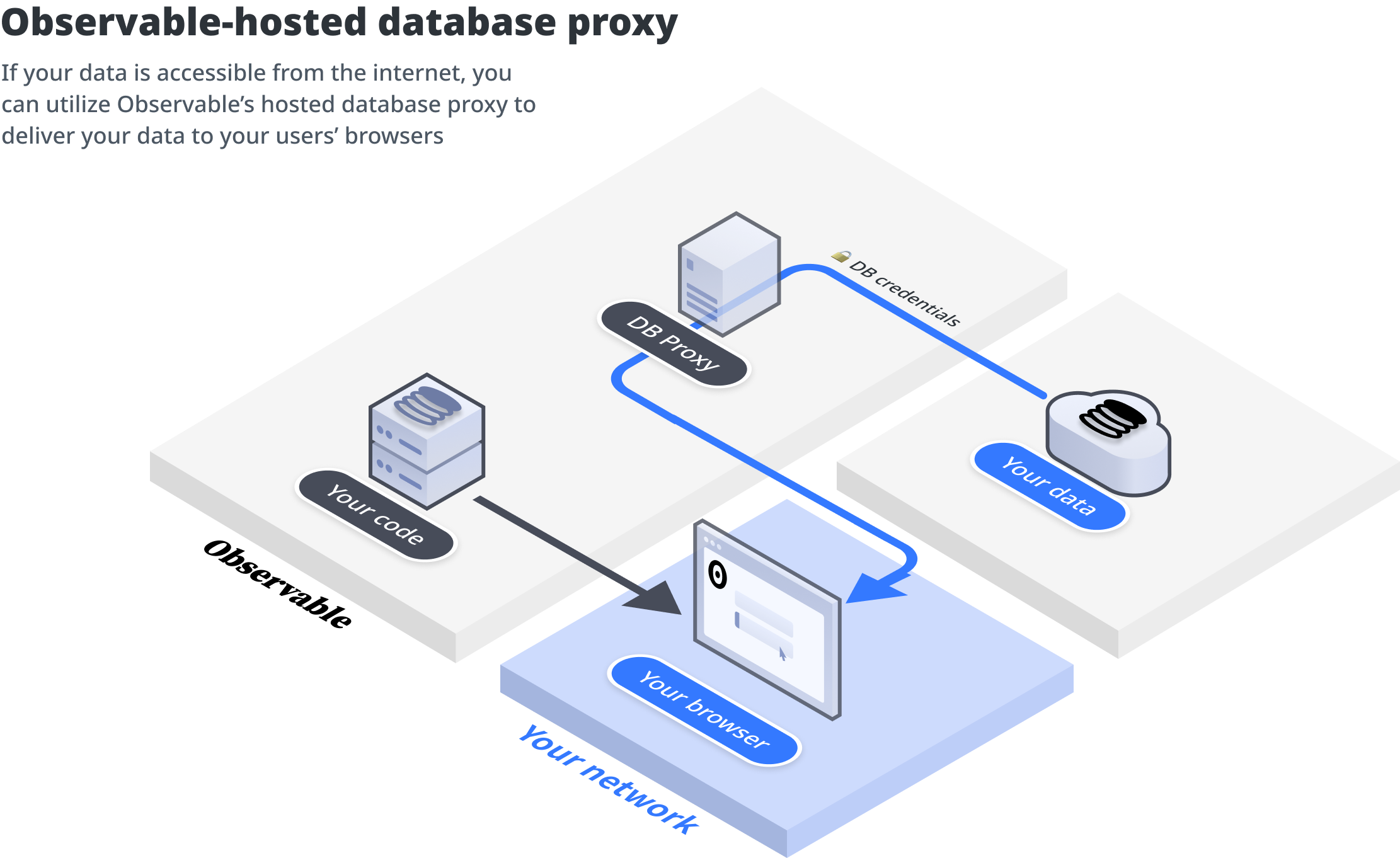
Observable protects user data by minimizing our data collection requirements and allowing users discretion over how to load data into notebooks. When users access data from external data sources, it does not exist on our servers. The data flows from the data source directly to the user's browser.
Please refer to this overview for more information about how our notebook architecture protects our users' data, as well as this summary about the options for connecting to data.
Q: Are stored secrets, data connectors, and cloud file attachments secure?
All user data, including stored secrets, data connectors, and authentication tokens for Cloud File Attachments, are encrypted at rest and entirely stored on our production systems. Our database is hosted by Heroku, and once an authentication token is set up into Observable, it cannot be re-downloaded or exported. Authentication tokens can be deleted at any time. Data accessed from a user's cloud files or databases are not stored on the Observable platform. Only access tokens required to authenticate with the sources are stored, encrypted, on Observable's servers. If the database is not accessible through the public internet, it can be accessed by installing a self-hosted database proxy on the same private network in which case data would flow from the source, through that proxy and to the browser without ever leaving the network.
Q: Does your application enable granular permissions and roles to be created?
In Observable Pro workspaces, owners can assign roles of 'owner', 'editor', or 'viewer' to team members. At the notebook level, team members can then control who within the team can view and edit the notebook. They can also share the notebook with the whole team as viewers or editors. Our Enterprise tier provides additional security and access controls. Enterprise workspace owners can configure limitations on who in the team can publish content and can require all team members to be authenticated against their domain(s), which protects their workspaces when members leave their organizations.
Q: Do you offer an on-prem solution?
Observable does not offer an on-prem solution. However, it is still possible to securely connect to data that cannot leave your private network, by installing a database proxy on your network. In this configuration, data travels from the source, through the proxy, and to the user's browser without ever having to leave the private network. We provide an open source Node.js database proxy for self-hosting. You can learn more about installing and using this proxy in this notebook.
Q: Do you use any sub-processors for data processing purposes?
No.
Q: Do all employees have access to user data?
No. It is our company policy to respect the principle of least privilege when designing access controls and administrative tools. For example: all employees have access to notebook metadata, but only support personnel have access to the content of the notebooks. In addition, all personnel are required to sign Confidentiality Agreements to protect customer information.
Q: Describe your security awareness program for personnel
Our employees are currently required to train on our company policies, which include:
Work Computer Policy: to properly secure employee endpoints
Secure Software Development Process: which describes how we design, build and deploy our software with security taken into consideration on every level
Security Incident Management Process: describing the steps and procedures that should be taken if an incident were to occur
Q: Do you scan for security vulnerabilities?
Our production infrastructure is hosted by Heroku, and is contained within Heroku’s secure network. Heroku regularly undergoes penetration tests and vulnerability assessments to ensure that the network remains secure. See: https://www.heroku.com/policy/security
Our software development process involves code vulnerability reviews by our developers in addition to resolution of issues flagged via automated vulnerability scanning. We monitor our codebase and dependencies for vulnerabilities using GitHub Enterprise’s advanced vulnerability scanning and are issued automated alerts when problems are found. See: https://github.com/features/security
Q: Do you conduct external (third-party) audits of the service? Are you SOC2 certified?
Not yet.